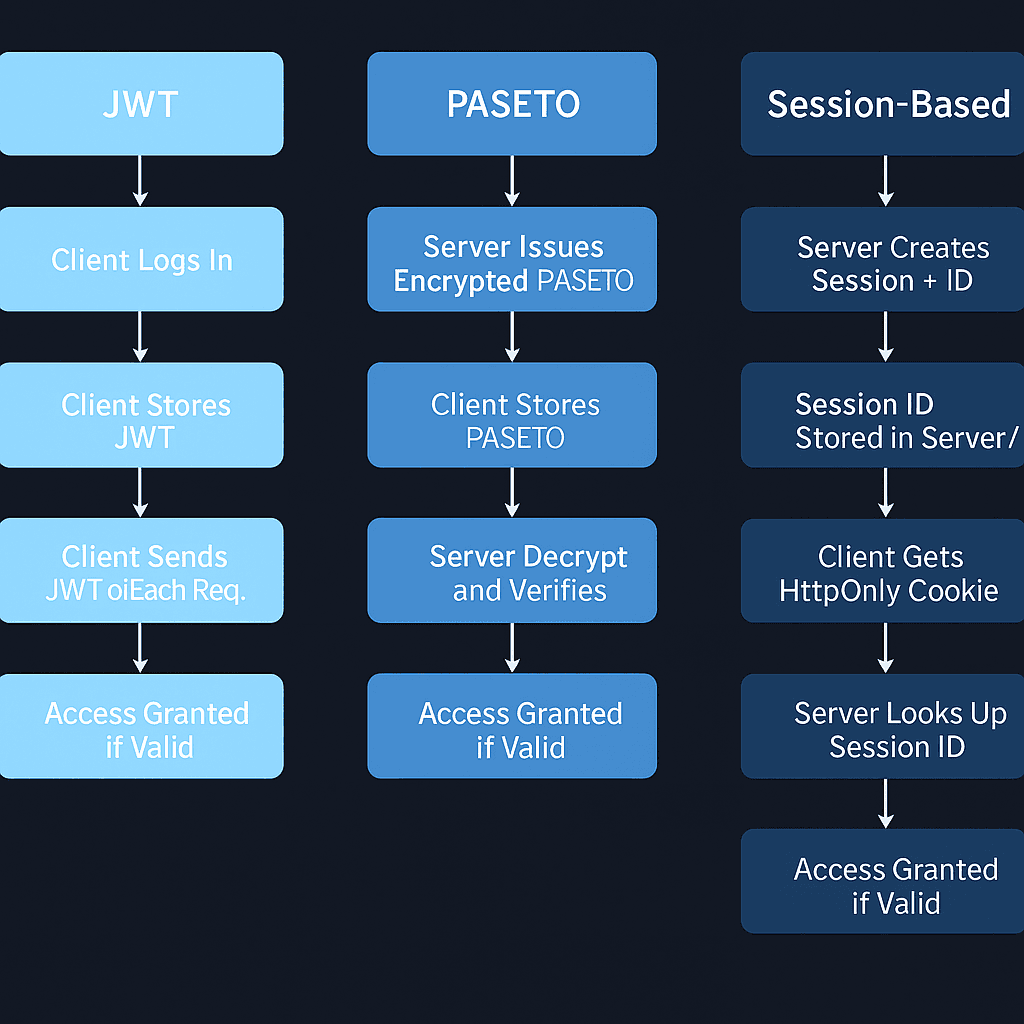
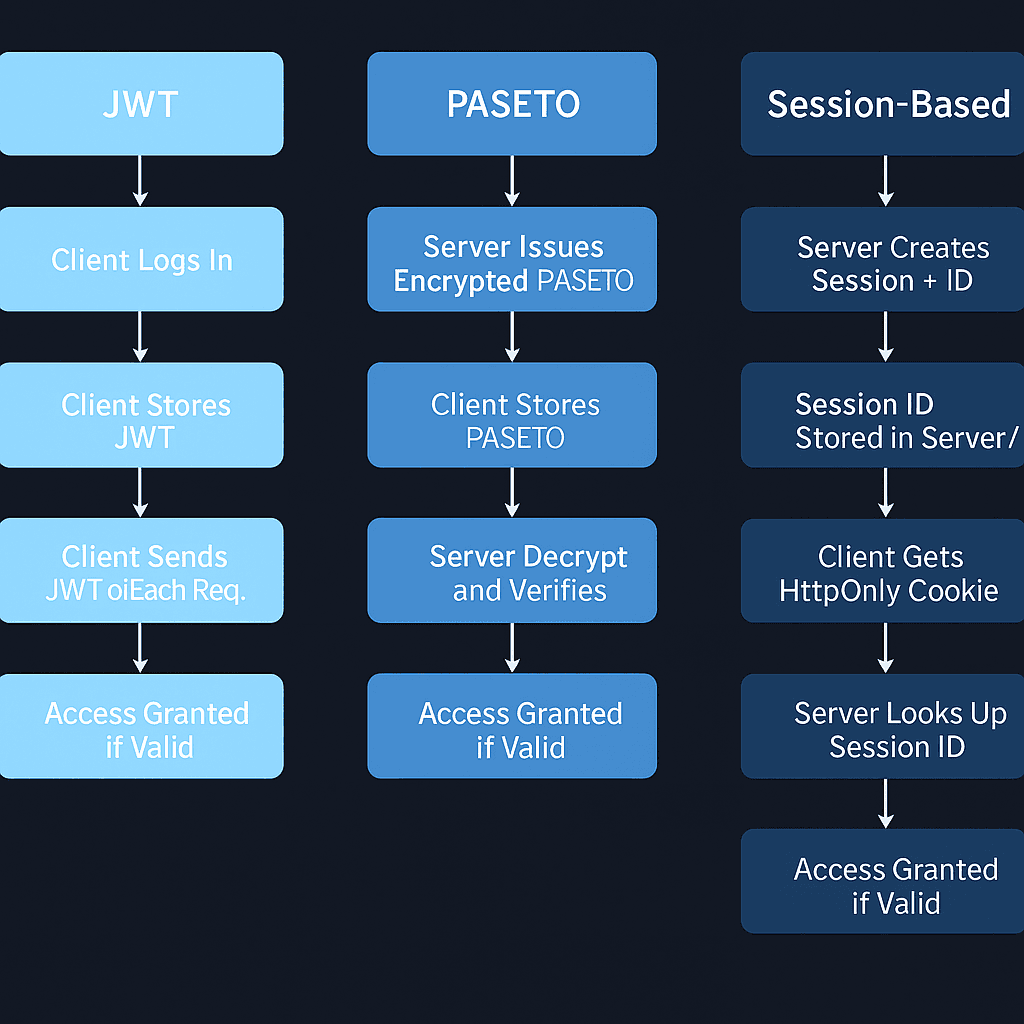
JWT vs PASETO vs Session-Based Auth
Secure Token Systems: What to Use and When
Jun 23, 20255 min read94
Search for a command to run...
Articles tagged with #jwt
Secure Token Systems: What to Use and When
JWTs are signed — but that doesn't make them safe from being reused by attackers

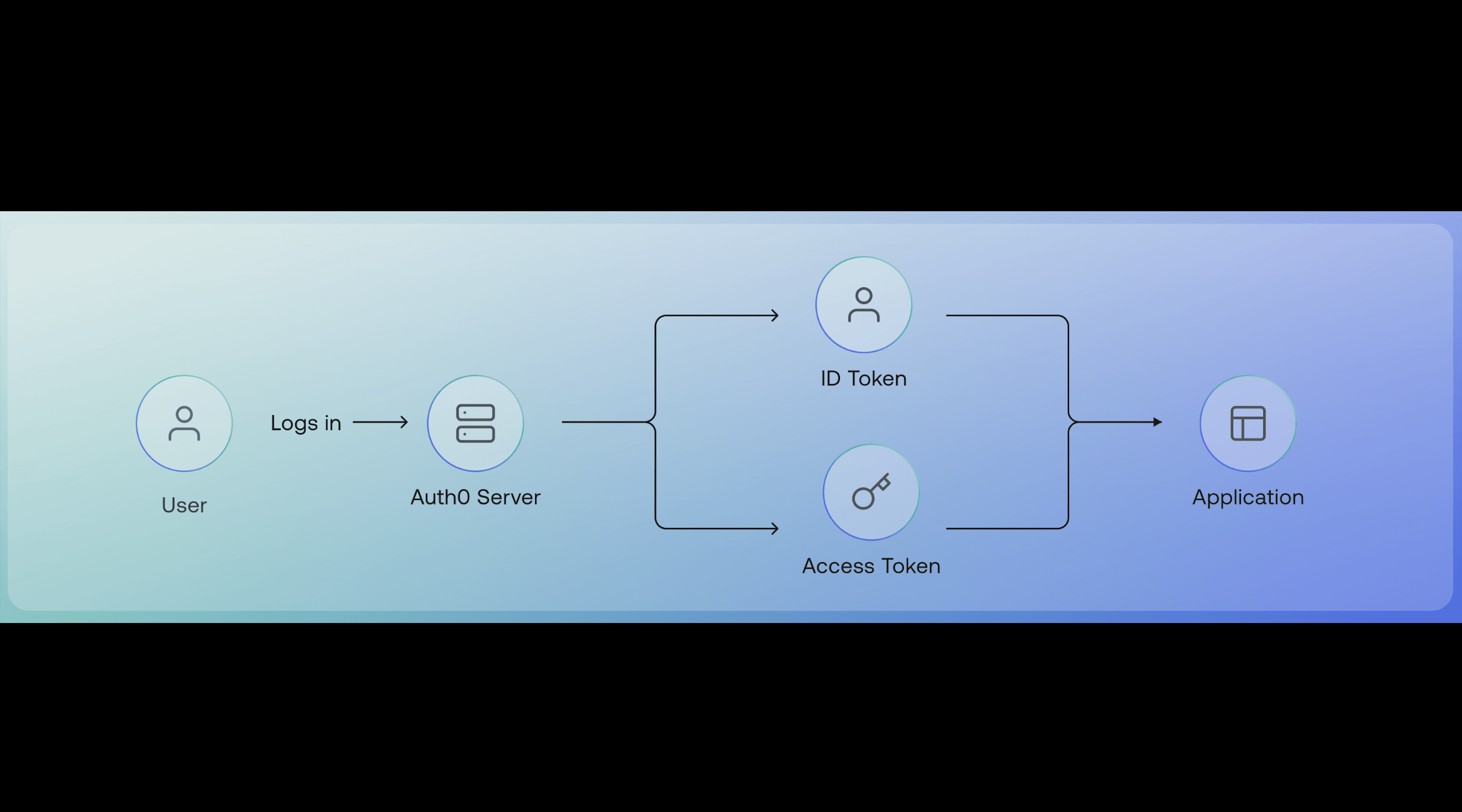
Understand How Token-Based Authentication and Encryption Work Behind the Scenes
Exploring JWTs, HMAC, and RSA Signing