What is Envelope Encryption?
A Practical Guide to understand Envelope Encryption

Principal Technical Consultant at GeekyAnts.
Bootstrapping our own Data Centre services.
I lead the development and management of innovative software products and frameworks at GeekyAnts, leveraging a wide range of technologies including OpenStack, Postgres, MySQL, GraphQL, Docker, Redis, API Gateway, Dapr, NodeJS, NextJS, and Laravel (PHP).
With over 9 years of hands-on experience, I specialize in agile software development, CI/CD implementation, security, scaling, design, architecture, and cloud infrastructure. My expertise extends to Metal as a Service (MaaS), Unattended OS Installation, OpenStack Cloud, Data Centre Automation & Management, and proficiency in utilizing tools like OpenNebula, Firecracker, FirecrackerContainerD, Qemu, and OpenVSwitch.
I guide and mentor a team of engineers, ensuring we meet our goals while fostering strong relationships with internal and external stakeholders. I contribute to various open-source projects on GitHub and share industry and technology insights on my blog at blog.faizahmed.in.
I hold an Engineer's Degree in Computer Science and Engineering from Raj Kumar Goel Engineering College and have multiple relevant certifications showcased on my LinkedIn skill badges.
Introduction
Encryption is essential for securing data, but managing encryption keys securely can be challenging.
Envelope Encryption is a widely used technique that enhances security by encrypting encryption keys rather than encrypting large amounts of data directly. It is commonly used in cloud security frameworks like AWS KMS, Google Cloud KMS, and Azure Key Vault.
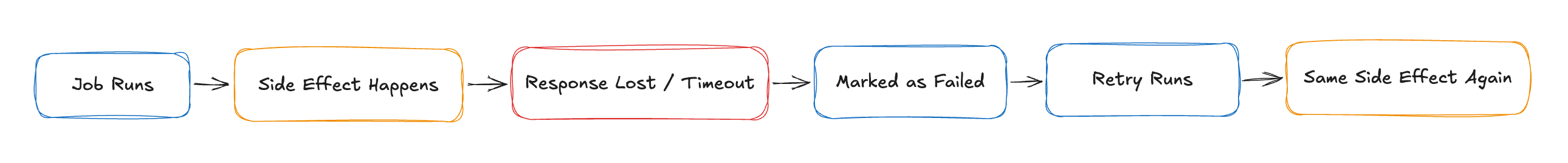
What is Envelope Encryption?
Envelope encryption is a method where:
A Data Encryption Key (DEK) is generated to encrypt the actual data.
The DEK is encrypted using a Key Encryption Key (KEK).
The encrypted DEK is stored alongside the encrypted data.
When decryption is needed, the KEK decrypts the DEK, and then the DEK decrypts the actual data.
Diagram: How Envelope Encryption Works
Why Use Envelope Encryption?
Pros & Cons
| Pros | Cons |
| Enhanced security: DEKs are never stored in plaintext | Adds complexity in key management |
| Faster performance: Only encrypts small DEKs | Requires an external Key Management Service (KMS) |
| Simplifies key rotation | If KEK is compromised, all DEKs are at risk |
Real-World Use Cases
Cloud Storage Encryption – AWS S3, Google Cloud Storage, and Azure Storage all use Envelope Encryption.
Database Encryption – Transparent Data Encryption (TDE) in databases like MySQL, PostgreSQL, and SQL Server.
Application Security – Secure API keys, secrets, and credentials in cloud environments.
How to Use AWS KMS for Envelope Encryption
AWS Key Management Service (KMS) supports Envelope Encryption with asymmetric keys (RSA, ECC) and symmetric keys (AES).
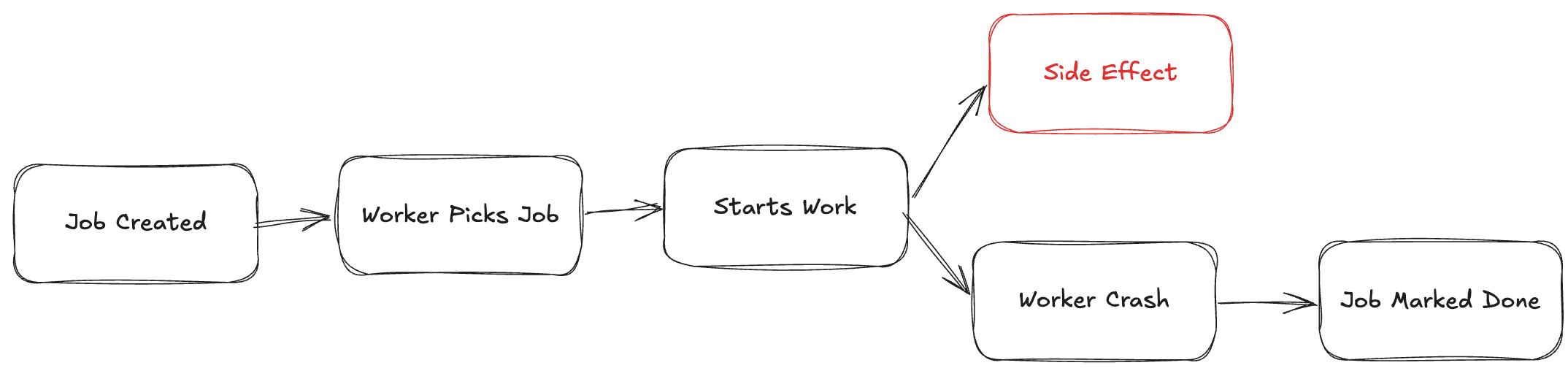
Steps to Encrypt Data using AWS KMS
Generate a Data Encryption Key (DEK) using AWS KMS.
Encrypt the Data using the DEK.
Encrypt the DEK using an AWS KMS-managed Key Encryption Key (KEK).
Store the Encrypted DEK alongside the encrypted data.
For decryption, retrieve and decrypt the DEK using KMS, then use the DEK to decrypt the actual data.
Mermaid Diagram: AWS KMS Envelope Encryption Workflow
AWS KMS Asymmetric Key Details
RSA Key Pairs (2048, 3072, 4096-bit) for encryption & digital signatures.
ECC Key Pairs (P-256, P-384, P-521) for lightweight cryptography.
IAM Policies & Grants control key access for security.
Use Cases: Secure API access, file encryption, authentication.
Conclusion
Envelope Encryption improves security and scalability by encrypting small encryption keys rather than large datasets.
AWS KMS, Google Cloud KMS, and Azure Key Vault provide built-in support for managing KEKs and automating encryption processes.
Implementing Envelope Encryption helps organisations enhance data protection, performance, and compliance.
Want a hands-on guide for AWS KMS implementation? Drop a comment below! 🚀
About Me 👨💻
I'm Faiz A. Farooqui. Software Engineer from Bengaluru, India.
Find out more about me @ faizahmed.in